Government IT
Staffing Agency
Most staffing firms treat government IT like any other tech placement. Post a job, scrape LinkedIn, send over whoever has the right acronyms on their resume. That works fine when you’re hiring for a SaaS startup. It falls apart completely when the role requires a security clearance, FISMA compliance knowledge, and someone who won’t bail after three months because they didn’t realize what working inside a SCIF actually feels like.

Why Government IT Hiring Is Different From Everything Else
Private sector tech hiring is competitive. Government IT hiring is competitive and complicated and wrapped in enough regulatory overhead that most staffing agencies just quietly avoid it because the effort-to-placement ratio looks terrible compared to dropping another React developer at a fintech startup. You’re not just matching skills to a job description. You’re matching skills to a job description inside a compliance framework that most recruiters have never even encountered, let alone understand well enough to screen candidates against.
FISMA, FedRAMP, NIST 800-53, ITAR. Those aren’t buzzwords to us. They’re the operating environment your new hire walks into on day one. And if your recruiter doesn’t understand what those acronyms mean in practice, they’re going to send you candidates who technically check the box on paper but have zero experience working inside the actual constraints of government systems.
Then there’s the clearance problem. About 70% of government IT roles require some level of security clearance. Secret, Top Secret, TS/SCI. The investigation process for a new clearance takes anywhere from four months to over a year depending on the level. That timeline is non-negotiable. The government runs it, not you, not us, not anybody. So if you need somebody cleared for a project starting in six weeks, you need somebody who already holds that clearance. Full stop.
That’s exactly the kind of candidate most generalist staffing firms can’t find. Because cleared IT professionals don’t typically hang out on job boards. They get recruited through networks. Referrals. People who know people. We’ve spent years building those relationships specifically.
Security Clearance Candidates Ready When You Need Them
Here’s what actually happens when a government contractor calls a generic IT staffing company looking for a cleared systems administrator. The recruiter goes to their database, filters for “security clearance,” and sends over three resumes. Two of the candidates held clearances five years ago that have since lapsed. The third has an active Secret but no experience with the specific agency environment the client needs.
Predictable. Our government IT recruiters maintain ongoing relationships with cleared professionals across multiple agencies and contractor environments. Active clearances. Current compliance experience. Not people who once worked on a government adjacent project and listed it creatively on their resume.
The clearance levels we recruit for include Secret, Top Secret, TS/SCI, and Public Trust. We also work with candidates who hold agency-specific credentials like DHS Suitability, IRS MBI, and DoD CAC.
But having a clearance isn’t enough by itself. We screen for actual hands-on experience with government IT environments. Can they navigate authority to operate processes? Have they worked inside continuous monitoring frameworks? Do they understand why you can’t just spin up an AWS instance the same way you would in the private sector? That’s what separates a cleared resume from a cleared person who can actually deliver. Most firms skip those questions entirely because their recruiters haven’t spent enough time in government environments to know what wrong answers sound like.

Government IT Roles We Staff
Infrastructure & Network Security
Systems administrators, network engineers, and infrastructure architects who understand government network segmentation, STIG hardening, and operating inside air-gapped environments. Not generalists. They know the difference between a standard enterprise network and one built to DISA compliance standards. The kind of people who have spent more time with STIG checklists than they’d admit at a dinner party, but that boring-sounding expertise is exactly what keeps classified networks from getting breached.
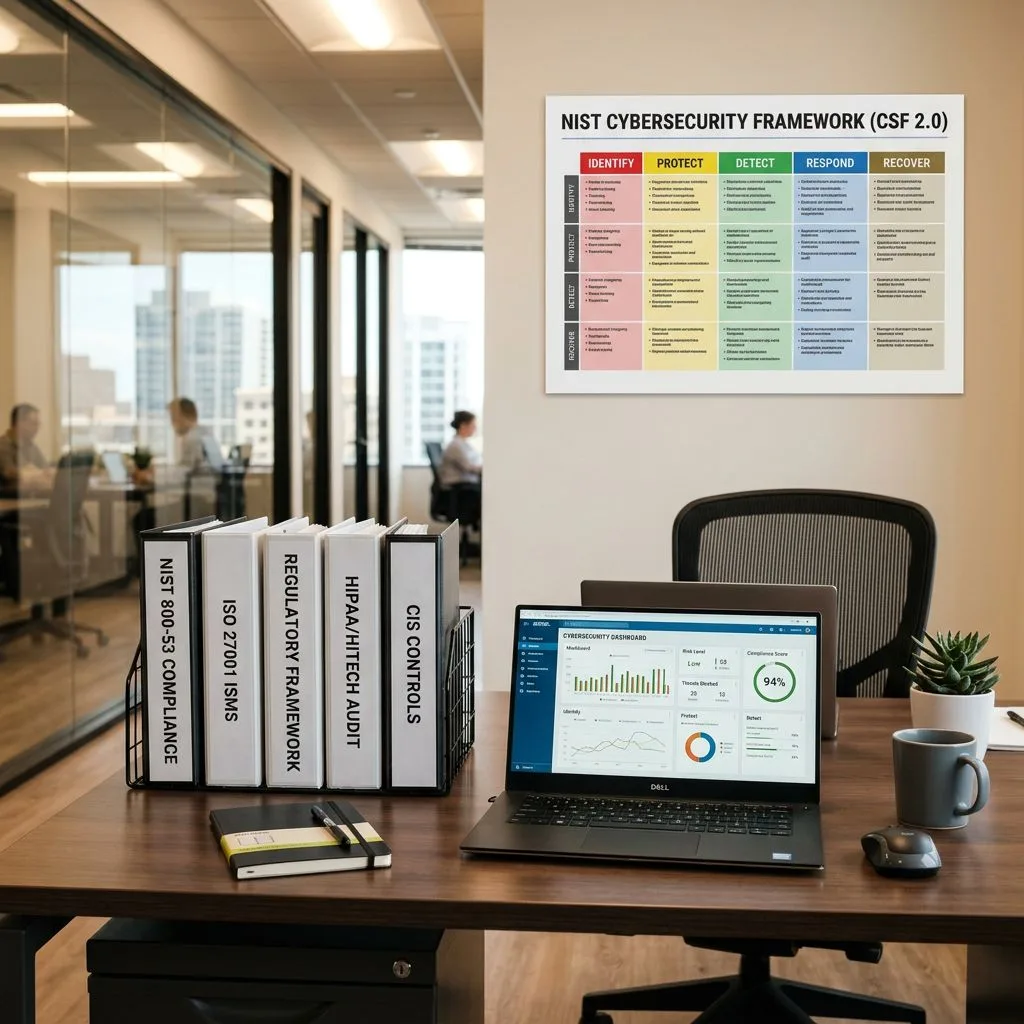
Cybersecurity & Compliance
Security analysts, compliance officers, GRC specialists, and SOC analysts with real experience in FISMA, FedRAMP, and NIST frameworks. The kind of people who have actually written system security plans, not just read about them. If your team needs to pass an ATO review, or if you’ve been sitting on a conditional ATO for six months because nobody on staff actually knows how to close the remaining POAMs without accidentally breaking the production environment in the process, these are the people you want in the room.
Cloud & DevSecOps
Cloud architects and DevSecOps engineers who work within FedRAMP-authorized environments. AWS GovCloud, Azure Government, Google Cloud for Government. They understand that “move fast and break things” does not apply when you’re operating inside an authorization boundary. Compliance-first cloud work requires a specific mindset and we recruit for it.
Data & Analytics
Data engineers, BI analysts, and data scientists who have handled CUI, PII, and classified datasets inside government systems. Data governance in public sector environments is its own beast. Classification rules, access controls, chain-of-custody requirements. Most commercial data teams have never had to think about what happens when a dataset contains information that technically can’t leave a specific network segment or when one wrong permission setting triggers a compliance incident that somebody has to explain to an inspector general. Different world entirely.

From Local Agencies to Prime Contractors
We work across the full government IT ecosystem. That means prime contractors staffing up for new task orders. Subcontractors who need specialized technical talent to fulfill their piece of a larger contract. State and local agencies modernizing legacy infrastructure. Civilian federal agencies running digital transformation initiatives that, candidly, should have started five years ago but got stuck in procurement limbo because that’s how government budgeting works sometimes.
The requirements look different at each level. Wildly different, actually. A prime contractor working a DoD program needs TS/SCI cleared network engineers who can start in two weeks. A county government upgrading its ERP system needs a project manager who understands public procurement and can work within budget cycles that don’t match the private sector calendar at all.
We’ve placed government IT professionals into defense, intelligence, civilian federal, state, and municipal environments. The common thread is that every placement requires understanding not just the technical requirements but the operational context. Timelines, compliance obligations, clearance logistics, budget constraints. Government IT staffing that ignores any of those factors isn’t really government IT staffing. It’s generic IT recruiting with a government label slapped on it.
Government IT Positions We Place
Not theoretical. Not aspirational. Every role listed here is one we’ve placed multiple times across federal, state, and local government environments.
- Systems Administrator (Windows/Linux)
- Network Engineer / Network Architect
- Cybersecurity Engineer
- SOC Analyst (Tier I/II/III)
- Information Security Analyst
- GRC Analyst (Governance, Risk, Compliance)
- Cloud Architect (AWS GovCloud / Azure Gov)
- DevSecOps Engineer
- Identity & Access Management (IAM) Engineer
- Data Engineer / BI Analyst
- IT Project Manager (PMP / Agile)
- Help Desk / Tier II Support (Cleared)
- Database Administrator
- CISO / VP of Information Security (Executive Search)

Why KORE1 for Government IT Staffing

Pre-cleared talent network. We maintain relationships with IT professionals who hold active Secret, Top Secret, and TS/SCI clearances. When you need somebody cleared, we’re not starting from zero.
Compliance-native recruiters. Our team understands FISMA, FedRAMP, NIST, ITAR, and the alphabet soup of frameworks that define government IT. We screen for compliance knowledge, not just technical skills.
Flexible engagement models. Contract, contract-to-hire, direct hire, project-based. Whatever fits. Government projects don’t all look the same and neither should the staffing model.
Fast placement against slow timelines. Government procurement moves slowly. Talent markets don’t. We bridge that gap by keeping warm pipelines of qualified, cleared candidates so when your contract award hits, you’re not scrambling.
14-day average time to first qualified candidates. Even for cleared roles.
Compliance Frameworks Our Candidates Know
Every candidate we submit for a government IT role is screened against the specific compliance requirements of that role. Not generic checkboxes. Real hands-on experience.
- FISMA (Federal Information Security Modernization Act)
- FedRAMP (Federal Risk and Authorization Management Program)
- NIST 800-53 / NIST Cybersecurity Framework
- ITAR (International Traffic in Arms Regulations)
- CMMC (Cybersecurity Maturity Model Certification)
- SOX (Sarbanes-Oxley, for financial systems)
- HIPAA (for healthcare-adjacent government systems)

Staffing Models for Government IT
Contract
Need cleared engineers for a task order that runs 6 to 12 months? Or a compliance specialist for an upcoming audit? Contract placements let you staff up for the work without committing to permanent headcount.
Contract-to-Hire
Government IT hires are high stakes. A security clearance doesn’t guarantee culture fit or performance. This model lets you evaluate somebody in the actual role environment before extending a permanent offer.
Direct Hire
For permanent roles like a CISO, security architect, or senior systems engineer. Our 92% 12-month retention rate reflects thorough vetting for both technical capability and long-term fit.
Project-Based
Cloud migrations to GovCloud. FedRAMP authorization projects. CMMC assessment prep. Some government IT work is finite and should be staffed that way.
Frequently Asked Questions About Government IT Staffing
What security clearance levels do your candidates hold?
We recruit candidates with active Secret, Top Secret, TS/SCI, and Public Trust clearances. We also work with candidates holding agency-specific credentials including DHS Suitability, IRS MBI, and DoD CAC. All clearance statuses are verified before candidate submission.
How long does it take to fill a cleared government IT position?
For roles requiring an existing clearance, we typically present qualified candidates within 14 business days. If a role allows for clearance sponsorship, the investigation timeline adds four to twelve months depending on the clearance level. We always clarify clearance requirements upfront so there are no timeline surprises, because discovering three months into a search that your “nice to have” clearance requirement is actually a hard gate is the kind of mistake that kills projects.
Do you work with federal agencies directly or just contractors?
Both. We staff government IT roles for prime contractors, subcontractors, and directly for state, local, and civilian federal agencies. The compliance and vetting requirements differ at each level and we adjust our process accordingly.
What compliance frameworks do your candidates have experience with?
Our government IT candidates work across FISMA, FedRAMP, NIST 800-53, NIST CSF, ITAR, CMMC, and SOX. We screen specifically for hands-on experience with these frameworks, not just familiarity. Our cybersecurity staffing practice handles the most security-intensive placements.
How is government IT staffing priced compared to commercial IT staffing?
Government IT staffing typically carries a modest premium over commercial rates, primarily because of clearance requirements and the smaller qualified candidate pool. Bill rates depend on clearance level, role seniority, location, and engagement model. We provide transparent pricing upfront with no hidden fees, because government procurement teams already deal with enough opaque billing from other vendors and the last thing they need is a staffing partner who buries markup in fine print.
Can you staff remote government IT positions?
Some government IT roles allow remote or hybrid work, particularly in civilian agencies and for roles that don’t require access to classified systems. Roles involving classified data or SCIF access are inherently on-site. We clarify work location requirements at the start of every engagement to ensure candidates match the physical access needs of the role.
Ready to Staff Your Government IT Team?
Whether you need cleared cybersecurity engineers for a DoD contract or systems administrators for a state agency modernization, KORE1 has the network and the expertise to deliver qualified candidates fast.

