Cloud Security Staffing: Why Every Business Needs It
Cloud security staffing is the process of recruiting and placing professionals who protect cloud infrastructure, data, and applications from threats, misconfigurations, and compliance failures. It sits at the intersection of two talent markets that used to be separate and are now inseparable: cloud engineering and cybersecurity.
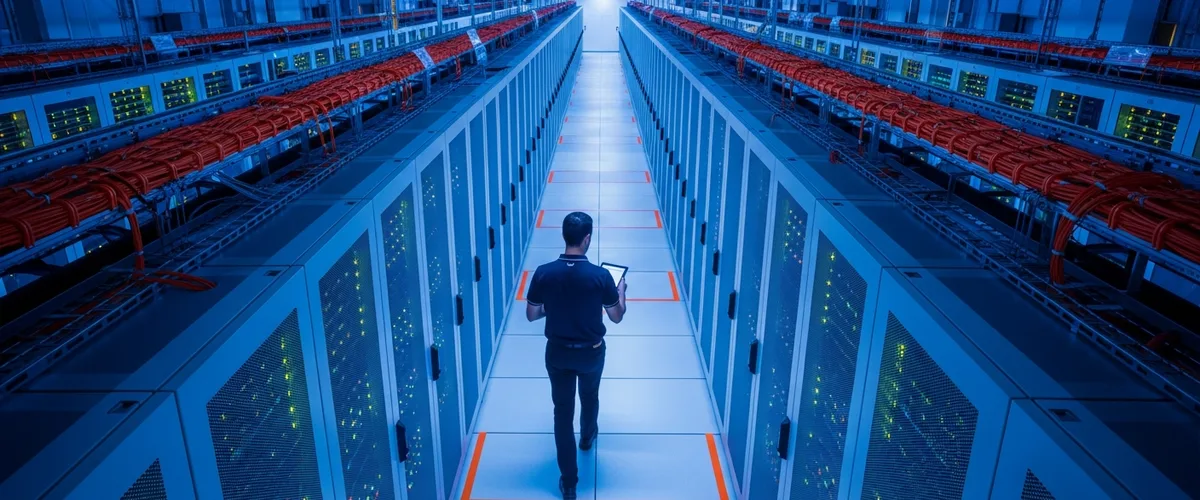
A client called us in February after a routine AWS audit turned up 14 publicly accessible S3 buckets. Not a breach. Not yet. But the kind of finding that ends careers if it becomes one. The person responsible for cloud security at that company was a network security analyst who had been handed AWS access six months earlier with no formal training, no CCSP, and no experience with IAM policy design. He knew firewalls. He did not know identity federation. The buckets were misconfigured on day one of the migration and nobody caught it because nobody on the team understood what “public” meant in the context of an S3 ACL versus a VPC security group. Two different mental models, one shared job title, and a six-figure incident waiting to happen.
Mike Carter, KORE1. I work across our IT staffing practice, and cloud security searches have become one of the faster-growing categories on my desk over the past eighteen months. Full transparency: we earn a fee when you hire through us. Some of what follows will push you toward that call. Some won’t. I’ll try to be obvious about which is which.
Why Cloud Security Is a Separate Hiring Problem
Five years ago you could hire a strong cybersecurity generalist and expect them to figure out AWS or Azure on the job. That worked when “cloud” meant a couple of EC2 instances and maybe an RDS database. It does not work now.
A cloud security engineer in 2026 needs to understand Kubernetes RBAC, container runtime security, identity federation across multiple IdPs, infrastructure-as-code scanning with tools like Checkov or tfsec, cloud-native SIEM integration, and the compliance mapping differences between SOC 2 Type II and FedRAMP Moderate. That is not a weekend of YouTube tutorials. That is two to three years of hands-on production work in a cloud-first environment, minimum.
The ISC2 2025 Cybersecurity Workforce Study surveyed 16,029 security professionals globally. Cloud security ranked as a critical skills need for 36% of respondents, just behind AI security at 41%. The overall cybersecurity workforce gap hit 4.8 million unfilled positions, a 19% jump in a single year. And for the first time in the study’s history, budget constraints passed talent availability as the top driver of staffing shortages. Companies aren’t just struggling to find cloud security people. They’re struggling to fund the search.
That budget squeeze matters more than the headline suggests. A company that can’t afford a $165K cloud security engineer doesn’t stop needing cloud security. It assigns the work to someone who already has a full plate and a different skill set. That is how you get 14 public S3 buckets, and a CISO who finds out about it from a pen test report three months later instead of from the team that created the problem in the first place.
The Roles That Fall Under Cloud Security Staffing
The title “cloud security engineer” gets used for at least four different jobs. Knowing which one you actually need cuts 30 days off the typical search.
| Role | Primary Focus | Key Tools / Platforms | Typical Base Salary |
|---|---|---|---|
| Cloud Security Engineer | Hands-on security implementation in AWS/Azure/GCP | IAM, GuardDuty, Security Hub, Terraform, Prisma Cloud | $136K – $167K |
| Cloud Security Architect | Designing security frameworks, zero-trust models, compliance mapping | Landing zones, SCPs, Azure Blueprints, network segmentation | $165K – $210K |
| Cloud SOC Analyst | Monitoring, triage, incident response for cloud workloads | Splunk, CrowdStrike Falcon, Wiz, CloudTrail, Sentinel | $95K – $130K |
| DevSecOps Engineer | Embedding security into CI/CD pipelines and IaC workflows | Snyk, Checkov, GitHub Advanced Security, OPA, Vault | $140K – $175K |
Salary ranges above draw from ZipRecruiter, Glassdoor, and Built In data as of early 2026. The variance between sources is $15K to $30K depending on the role, which tells you something about how inconsistently this market is priced.
The mistake we see most often: a company posts a “Cloud Security Engineer” req but the JD describes an architect. The budget says $140K. The work says $185K. The search stalls at week four. The hiring manager blames the market. The market is fine. The job description is doing two things at once and the budget only covers one of them.

What Makes Cloud Security Hiring Different from General Cybersecurity
General cybersecurity staffing and cloud security staffing overlap, but treating them as the same search is how companies end up with the wrong person in the seat.
A traditional cybersecurity hire thinks in terms of perimeter defense, endpoint protection, SIEM rules, and incident response playbooks. Good skills. Real skills. But cloud environments don’t have a perimeter in the traditional sense. The “perimeter” is an IAM policy attached to a role that got created by a Terraform module that a developer wrote nine months ago and nobody has reviewed since. The attack surface is not a network boundary. It is every API call, every misconfigured service principal, every overly permissive role assumption chain.
We ran a cloud security search last fall for a fintech client in Irvine. They had interviewed six candidates from their existing cybersecurity recruiting pipeline. All six had strong SIEM backgrounds. Three had CISSP certifications. None of them could explain how AWS STS AssumeRole works or why a cross-account trust policy matters for their microservices architecture. The client had been screening for “security” and missing “cloud.” The person we ultimately placed came from an SRE background, had picked up security through two years of running a cloud-native SOC at a SaaS company, and held the AWS Security Specialty certification. Different career path. Different screening criteria. Right hire.
The Bureau of Labor Statistics projects 29% growth for information security analysts through 2034, with about 16,000 annual openings and a median wage of $124,910. Those are strong numbers, and they understate the cloud-specific demand because BLS doesn’t break out cloud security as a separate category. The people who can do both cloud infrastructure and security at production scale are a subset of that 29% growth figure, and the subset is a lot smaller than the headline.
The Certification Question
Certs matter in cloud security hiring. Not all of them. Not equally. Here is what we actually screen for and why.
- CCSP (Certified Cloud Security Professional) from ISC2. This is the gold standard for cloud security, and it shows. CCSP holders average $148,009 annually according to PayScale, which is a 33% premium over non-certified cloud professionals. It requires five years of cumulative IT experience including three years in security and one in cloud. You are not getting paper tigers with this cert. The updated 2026 exam domains cover everything from cloud data security to legal compliance across jurisdictions.
- AWS Security Specialty. Probably the single most useful signal for hands-on cloud security work in AWS-heavy shops. The exam tests real implementation knowledge: KMS key policies, VPC flow log analysis, GuardDuty finding remediation. We have had candidates fail this exam twice and pass the CISSP on the first try, which tells you about the gap between conceptual security knowledge and cloud-specific implementation.
- CCSK (Certificate of Cloud Security Knowledge) from the Cloud Security Alliance. Lighter weight than CCSP. Average salary is $121,932. We treat this as a baseline signal, not a differentiator. Useful for junior cloud security hires and career-changers who haven’t accumulated the experience hours for CCSP yet.
- Azure Security Engineer Associate, GCP Professional Cloud Security Engineer. Platform-specific. Useful when you know your stack. Not a substitute for the broader frameworks above.
Here is something that took us a few bad shortlists to figure out. A candidate with CISSP plus hands-on cloud production experience is often a stronger hire than a candidate with CCSP but no production time in your specific cloud provider. Certifications tell you someone studied. Deployment history tells you someone shipped. We screen for both.
What a Cloud Security Breach Actually Costs
The IBM 2025 Cost of a Data Breach Report put the global average at $4.44 million per breach. That number dropped 9% from the prior year, and IBM credits AI-powered detection tools for the improvement. Good news, sort of.
The less-good news. Breaches involving multiple cloud environments averaged $5.05 million, more than a million above the on-premises average of $4.01 million. US organizations specifically face $10.22 million on average, a record. And shadow AI, the unsanctioned use of AI tools by employees, showed up as a factor in 20% of breaches, adding $670,000 to the average cost.
97% of AI-related breaches happened at organizations without proper AI access controls.
None of those numbers include the reputational cost, the customer churn, or the three-to-six months of executive distraction that follows a public incident. A single cloud security engineer at $150K fully loaded is roughly 3% of the average US breach cost. The math is not complicated. It just gets ignored until the finding shows up in a pen test or an auditor’s report.

How Cloud Security Staffing Through an Agency Works
The process is different from general IT recruiting because the vetting has to be different. Here is how it works when a company brings a search to us at KORE1, and how it should work regardless of who you use.
Intake is longer than you expect. A general IT staffing req can be scoped in a 30-minute call. Cloud security intake takes 60 to 90 minutes because we need to understand the cloud architecture, the compliance framework (SOC 2, HIPAA, FedRAMP, PCI-DSS), the existing team’s gaps, and whether the role is hands-on implementation or strategic architecture. Skip this step and every shortlist will miss.
The sourcing pool is different too. Cloud security candidates are not sitting on job boards. The strong ones are employed, usually at cloud-native companies or consulting firms, and they change jobs for one of three reasons: comp, scope, or frustration with the security maturity of their current org. Our cloud engineer staffing pipeline and our cybersecurity staffing pipeline both feed into cloud security searches, which is why having separate dedicated pipelines for each matters. A generalist recruiter searching LinkedIn for “cloud security engineer” is competing with every other generalist recruiter doing the same keyword search. The results are predictable, and by predictable I mean you get twenty resumes from people who listed “cloud” on their LinkedIn because they once logged into the AWS console during a demo.
Technical screening is where agencies earn or lose credibility. We test for architecture diagramming, not just tool knowledge. Can the candidate whiteboard a zero-trust network architecture for a multi-account AWS organization? Can they explain why you would use AWS Organizations SCPs instead of IAM permission boundaries for a specific guardrail, and when you’d use both? Can they walk through a CloudTrail log and identify the three API calls that indicate a compromised role assumption? If your recruiter can’t evaluate those answers, the shortlist is a keyword match, not a skills match.
Time-to-fill for cloud security roles through our desk runs about 25 to 35 days for contract placements and 40 to 55 days for direct hire. General cybersecurity roles are faster, 15 to 25 days for contract, because the candidate pool is larger and the skills are more standardized. The delta is real and it reflects the specialization depth.
Building a Cloud Security Team from Scratch
If you’re standing up cloud security as a function for the first time, the order matters more than the titles.
Hire the architect first. Not the engineer. The architect sets the framework, the guardrails, the compliance mapping, and the tooling strategy. Without that foundation, every engineer you hire afterward is making ad hoc decisions that will need to be unwound in eighteen months when you realize nobody agreed on a tagging standard, a logging strategy, or a secrets management approach.
Second hire should be a cloud security engineer, hands-on, implementing what the architect designed. This is the person writing the Terraform modules for security baselines, configuring GuardDuty and Security Hub, building the automated remediation workflows for common misconfigurations. They need production experience in your primary cloud provider. Do not compromise on this. A strong AWS person who “can learn Azure” is six months away from being productive in Azure security. That is six months of coverage gaps.
Third hire depends on your scale. Under 500 cloud workloads, a DevSecOps engineer who embeds security into CI/CD is probably more valuable than a dedicated SOC analyst. Over 500 workloads, or if you’re in a regulated industry, you need the SOC analyst first because the alert volume will overwhelm anyone doing it as a side task.
Companies that try to hire all three at once usually end up with one good hire and two compromises, because they burn their referral network and their recruiter’s pipeline in a single sprint. Stagger the searches by 30 days.
Contract vs. Direct Hire for Cloud Security Roles
Both models work. The right one depends on what you’re solving for.
Contract staffing makes sense when you need cloud security expertise for a specific project: a cloud migration, a SOC 2 audit, a post-breach remediation, or a FedRAMP authorization push. These engagements have defined timelines, usually three to nine months, and the work doesn’t require someone who will grow into a long-term organizational role. Contract rates for senior cloud security engineers run $85 to $130 per hour depending on the certification stack and the compliance domain. That sounds expensive until you compare it to the fully loaded cost of a full-time hire you don’t need past Q3.
Direct hire is the right model when cloud security is a permanent function and the person you’re hiring will own ongoing architecture decisions, compliance posture, and team-building. Most of our direct-hire cloud security placements are at companies where the cloud footprint is large enough that the role justifies itself permanently, usually $2M or more in annual cloud spend.
One hybrid approach that has worked well for three of our clients in the last year: bring a senior cloud security engineer on contract for six months to build the foundation, then convert to direct hire if the fit is right. The contract period gives both sides a real working evaluation instead of a four-interview guessing game. Contract-to-hire conversion rates for cloud security roles through our desk run about 70%, which is higher than our overall average because the specialization makes cultural mismatches rarer. When someone can actually do the cloud security work, the fit question usually answers itself.
Why Companies Get This Wrong
The most common mistake is not a bad hire. It is no hire. The ISC2 study found that 67% of organizations are short-staffed on cybersecurity, and 88% experienced a significant security event at least partly because of skills gaps. Those aren’t abstract numbers. That is the S3 bucket, the overpermissive IAM role, the CloudTrail logging that was turned off to save $200 a month and nobody noticed for eleven weeks.
Second most common mistake: hiring a traditional security person and hoping they’ll pick up cloud. Some do. Many don’t. The ones who don’t tend to apply on-premises mental models to cloud environments, which leads to things like running network-based IDS in a VPC and calling it cloud security. It is not. Cloud-native threats are identity-based, not network-based. The tooling is different, the attack patterns look nothing alike, and the remediation workflows assume a level of cloud-native fluency that most traditional security analysts simply have not built yet because they never needed to until their company moved to AWS or Azure.
Third mistake: over-indexing on certifications and under-indexing on production experience. I’ve seen hiring panels reject candidates who had been running cloud security at scale for four years because they didn’t have the CCSP, while approving candidates who had the cert but had never configured a real CloudTrail-to-SIEM pipeline. The cert is a signal. The production history is the proof.
Before You Start Hiring
So what does a cloud security team actually need to look like?
Depends on your cloud spend and your compliance requirements. Under $1M annually in cloud spend, one strong cloud security engineer is probably enough if they have architecture-level judgment. Between $1M and $5M, you are looking at two people minimum, an architect-level lead who sets the guardrails and a hands-on implementer who builds them into the infrastructure every day. Over $5M, or in a regulated industry, you’re building a team of three to five, plus tooling budget for CSPM, CWPP, and SIEM.
Realistically, how long does it take to fill a cloud security role?
25 to 35 days for contract through an agency. 40 to 55 days for direct hire. DIY searches without a dedicated cloud security pipeline tend to run 60 to 90 days because the early shortlists are full of general cybersecurity candidates who don’t have the cloud depth. The ISC2 gap numbers are real. This market is tight, and it’s been tight for three years running.
Is the CCSP actually worth screening for, or is it just credential inflation?
Worth it. The five-year experience requirement filters out paper chasers, which is why CCSP holders average $148K versus $122K for CCSK. But I wouldn’t reject a candidate who has four years of production cloud security experience and no CCSP over a candidate who has the cert and eighteen months of experience. The cert accelerates the conversation. The experience closes the hire.
Can a company just train its existing cybersecurity team on cloud?
Sometimes. It takes 12 to 18 months to get a traditional security professional productive in cloud security at a senior level, assuming they’re motivated and the company invests in real training, not just a Udemy subscription. That timeline works if you’re not currently migrating to the cloud, not facing an audit, and not already behind on your cloud security posture. If any of those three are true, you need someone who can start producing on day one, which means an external hire.
What’s the actual fee structure for cloud security staffing through an agency?
Contract: markup on the hourly bill rate, typically 30% to 45% depending on the role complexity and contract length. Direct hire: a percentage of first-year base salary, usually 20% to 25% for cloud security roles. Yes, that’s $30K to $40K on a $160K placement. Whether that fee is worth it depends on whether your internal recruiting team can source, screen, and close cloud security candidates in a competitive timeline. For most companies we talk to, the answer is no, because the candidate pool is small enough that general-purpose recruiting approaches don’t work. For companies with a mature internal TA function and an existing cloud engineering pipeline, doing it yourself is a legitimate option. We’ll tell you that on the intake call if it’s true.
Get Cloud Security Staffing Right the First Time
The gap between companies that have cloud security staffing figured out and companies that are winging it is widening every quarter. Cloud adoption grows. The threat landscape grows with it. The talent pool grows slower than both. ISC2’s 4.8 million global gap isn’t shrinking. If anything, the cloud-specific slice of that gap is growing faster than the overall number because every company that moves workloads to the cloud inherits a security surface they didn’t have before.
If you’re running a cloud migration, a compliance push, or just realizing that nobody on your team actually owns cloud security as a primary responsibility, that’s the signal to staff for it. Not after the audit finding. Not after the incident. Now.
Talk to our team about your cloud security hiring needs. We will be straight with you about whether an agency makes sense for your particular situation, and if it doesn’t, you’ll hear that from us before you hear a pitch.