The Talent Market Is Worse Than Most People Realize
I’m going to throw some numbers at you. They’re from the 2025 ISC2 Cybersecurity Workforce Study, which surveyed 16,029 security professionals globally and is the most comprehensive annual look at the state of this workforce.The active global cybersecurity workforce sits at 5.5 million people. The unfilled gap is 4.8 million. That gap grew 19% in one year. The workforce grew 0.1%.Let that sink in. The shortage is almost as large as the entire existing workforce. And it’s getting bigger roughly 190 times faster than the workforce is growing. BLS projects 33% employment growth for information security analysts through 2033, which is six times the national average for all occupations. So no, this isn’t going to self-correct.What shifted this year is interesting. For the first time in the ISC2 study’s history, budget constraints passed talent availability as the top driver of staffing shortages. A third of organizations told ISC2 they don’t have the budget to staff security properly. Another 29% said they can’t afford people with the skills they actually need. Budget cuts hit 36% of orgs. Layoffs hit 24%. Hiring freezes affected 49% of large organizations. All while threats are escalating and compliance requirements keep expanding.That’s the squeeze. More risk, less money, fewer people. And the people you do have might not have the right skills.Here’s the stat that should alarm you most. 88% of organizations experienced at least one significant cybersecurity event because of skills gaps. Not staffing gaps. Skills gaps. ISC2 was deliberate about that distinction. Nearly 70% had more than one incident. Even fully staffed teams are getting hit because they lack specific expertise, especially in AI security and cloud. Hiring more bodies doesn’t solve the problem if those bodies don’t have the skills you need.Oh, and hiring timelines? Over a third of organizations report three to six months to fill security roles regardless of seniority level. Half say they struggle to keep people once they manage to hire them.What You Should Actually Be Paying
Your salary data might be wrong. Seriously. If it’s from 2023 or even early 2024, it’s probably 15 to 25% below where the market is today. Cybersecurity comp moves 7 to 10 percent per year depending on the role. The IANS and Artico Search CISO benchmark found that CISO compensation grew 6.7% in 2025 alone, outpacing security budget growth of just 4%. That gap between what leaders cost and what companies budget for them keeps widening.We compiled data from BLS, Glassdoor, the IANS benchmark, and the Programs.com 2026 salary analysis. Here’s the picture.
| Role | Experience | Salary Range | What We’re Seeing |
|---|---|---|---|
| SOC Analyst | 0-2 yrs | $70K – $100K | Security+ bumps the low end 10-15% |
| Security Engineer | 3-5 yrs | $110K – $148K | 20-30% jump from junior roles. Pretty standard transition. |
| Cloud Security Engineer | 3-7 yrs | $128K – $175K | Hardest to fill. 36% of orgs say cloud is their biggest gap. |
| Security Architect | 7+ yrs | $152K – $220K | Glassdoor 90th percentile hits $259K. Zero-trust skills push toward that ceiling. |
| Pen Tester | 3-7 yrs | $110K – $160K | Reverse engineering takes it past $190K. |
| Cybersecurity Manager | 7+ yrs | $135K – $170K | Compliance overlay adds $10-20K |
| CISO | 15+ yrs | $220K – $420K+ base | Total comp $250K-$700K. Top 1% clears $3.2M. Equity = half the package in tech. |
Skills to Screen For

- CISSP. Gold standard. 22 to 35% salary premium over non-certified peers. If you’re hiring for any senior security role and you don’t see CISSP on the resume, you’ll probably pay less, but you’ll also lose out on a lot of strong candidates who filter for roles that require it.
- CISM. Management and governance. Consistently one of the highest-paying security certs. If you’re hiring a security manager or director, this is the one you want to see.
- CEH. First cert most employers look for in pen testing hires. Solid foundational credibility for offensive security.
- AWS and Azure security specialties. Becoming table stakes for cloud roles. Push compensation past $160K.
- Security clearances. Technically not a cert. But clearances create an entirely separate hiring market with its own salary bands. If you need cleared security professionals for government or defense-adjacent work, it’s a whole different search.
These Are Not the Same Job
We get calls from companies that say they need to hire “a cybersecurity person.” Every time, my first question is the same. What kind? Because cybersecurity isn’t one job. It’s a dozen different jobs under one umbrella, and hiring the wrong type is like calling a dermatologist when you need an orthopedic surgeon.Security Analyst. Frontline SOC work. Monitoring networks, triaging alerts, investigating weird stuff. Many work shifts because attacks don’t wait for business hours. This is where a lot of security careers start, and there’s nothing wrong with that. But experienced Tier 3 analysts who actually do threat hunting are genuinely hard to find and worth more than most companies want to pay them.Security Engineer. Builds and maintains the infrastructure itself. Firewalls, authentication, encryption, endpoint protection. If the analyst watches the cameras, the engineer installed them and wired the whole building.Security Architect. Top of the technical pay scale and it’s justified. These are the people designing systems that prevent catastrophic breaches. A bad architectural decision can expose millions of people and cost tens of millions of dollars. You want this hire to be the best person you can afford. This is not where you cut corners.Penetration Tester. Ethical hackers trying to break your systems before someone else does. Requires deep technical skill and genuine creativity. The best pen testers think like actual attackers, which honestly makes them a little unusual in traditional interview settings. That weirdness is the point. If they think like everyone else, they won’t find what everyone else misses.Incident Responder. When things go sideways, these people contain the damage and lead recovery. Calm under pressure is not just a nice-to-have for this role. It IS the role. Fast decisions, incomplete data, high stakes, everyone around them stressed. Not everyone has the temperament for this. I’d estimate maybe 20% of the security professionals I’ve worked with would thrive in a pure incident response position.CISO. Leads the whole program. Teams, policies, compliance, board reporting, vendor oversight, incident management. The skill that makes or breaks a CISO isn’t technical depth. It’s the ability to frame cyber risk in financial and legal terms that a board of directors can act on. We had a search last year where the client passed on a technically stronger candidate and hired someone with half the certifications but twice the communication ability. Best hire they made all year, by their own admission six months later.What to Do When There Aren’t Enough Candidates
You already know the default process doesn’t work. Post a job. Get flooded with unqualified applications. Cherry-pick the five that look decent. Lose three of them while scheduling the next interview round. Offer the fourth. They counter with another company’s number. You go back to square one.When there are 4.8 million more openings than people, you have to change the approach. Here’s what we’ve seen actually move the needle.Stop filtering so aggressively on background. This one gets me every time. Ninety percent of hiring managers only consider candidates with previous IT experience. But people coming from networking, system administration, and software development transition into security roles all the time. And women and minorities are seriously underrepresented in cybersecurity, which means there’s a huge talent pool that most companies aren’t even reaching. If your sourcing strategy only produces candidates who look like the last person in the role, you’re making the problem worse than it needs to be.Develop the people you already have. ISC2’s whole theme this year was that the cybersecurity workforce challenge isn’t solved just by adding headcount. It’s about developing skills within existing teams. Someone who already knows your environment, your tools, your business, they can learn cloud security or incident response faster than an outside hire can learn all of that context about your company. And it helps retention because people stay where they’re growing. Two birds.Use contract talent where it makes sense. Not every security need requires a permanent hire. Compliance audits, pen testing engagements, covering a gap during a transition, handling a specific project with a defined endpoint. Contract cybersecurity professionals give you flexibility when budgets are tight and needs are specific. An IT staffing partner can source qualified people much faster than an internal job posting.Build pipeline through schools. Longer play. Worth it. Internship programs and university partnerships give you access to talent before the market competes for them. Cybersecurity bootcamps are producing competent entry-level candidates now too. A couple of our clients started doing this two years ago and they’ve hired four people out of their own intern programs since then. Not massive numbers, but four roles they didn’t have to search for at all.Move your process faster. I cannot stress this enough. The industry average to fill a cybersecurity role is three to six months. That timeline guarantees you lose top candidates. The companies that actually close these hires do it in three to four weeks. And that doesn’t mean rushing or cutting corners. It means having your comp range approved before the search starts. Having your interview panel locked. Eliminating the two-week gaps between rounds where nothing happens and the candidate gets antsy. You’d be amazed how many great candidates we’ve seen walk away not because the offer was bad but because the process was so slow they assumed the company wasn’t serious.Mistakes We Keep Seeing
Four things. All avoidable. All expensive.
When Outside Help Is Worth It (and When It Isn’t)
I’m going to be straightforward about this since we’re a firm that does this for a living.If you need one generalist SOC analyst and your internal recruiting team has experience hiring security people, do it yourself. You probably don’t need us and the fee isn’t worth it for a straightforward search.But. There are situations where a specialized cybersecurity staffing partner genuinely changes the outcome. Here’s when.Somebody just left and it’s urgent. Your lead security engineer gave notice. Or you found a vulnerability that requires skills nobody on the current team has. You can’t sit with a three-to-six-month hiring process. A staffing partner can have qualified people in front of you in days. That speed has real value when you’ve got open exposure.You need a niche skill that doesn’t appear on job boards. Cloud pen testers. AI/ML security engineers. Compliance specialists who know your specific regulatory environment inside and out. These professionals do not apply to LinkedIn postings. They get recruited through networks that specialized engineering staffing firms build over years.Your CFO wants budget flexibility. Contract and contract-to-hire models let you add security capability without permanent headcount. Your CFO gets the flexibility they want. Your CISO gets the coverage they need. Both are right.You need comp data and market intelligence. What’s the going rate for a senior cloud security engineer in Orange County versus Dallas? Are candidates expecting equity? What are the deal-breakers in your interview process? We have this data because we run dozens of security searches simultaneously. It makes your offers land better and your process waste less time.Quick Section on Retention
Because honestly, keeping people might be harder than finding them.Good news first. 68% of cybersecurity professionals report being satisfied with their current jobs, up from 2024. And the strongest satisfaction drivers are teams (78%) and direct managers (73%). Not compensation. Not company brand. The people they work with and the person they report to. Think about what that means for how you structure your security org.Career pathing. Nearly a third of ISC2 respondents said advancement opportunities are critical to their engagement. Security has a bunch of directions people can go. Technical depth, management, architecture, consulting, risk advisory. If someone can see where they’re headed at your company, they stick around. If they can’t, they start taking recruiter calls. Not complicated and not expensive to fix. But you do have to actually build the paths, not just talk about them during onboarding and never mention them again.Burnout. 48% feel exhausted trying to keep up with threats and new tech. 47% feel overwhelmed by workload. These are people defending your organization 24/7 against adversaries who literally never stop. You cannot just keep piling work on a short-staffed team and expect them to absorb it indefinitely. At some point they leave. And then you’re even more short-staffed. We see this cycle repeat constantly. Distribute the load. Set realistic expectations. Fund training during working hours, not as weekend homework. The companies that handle this well keep their people. The companies that don’t keep calling us to backfill the same positions at higher and higher salaries.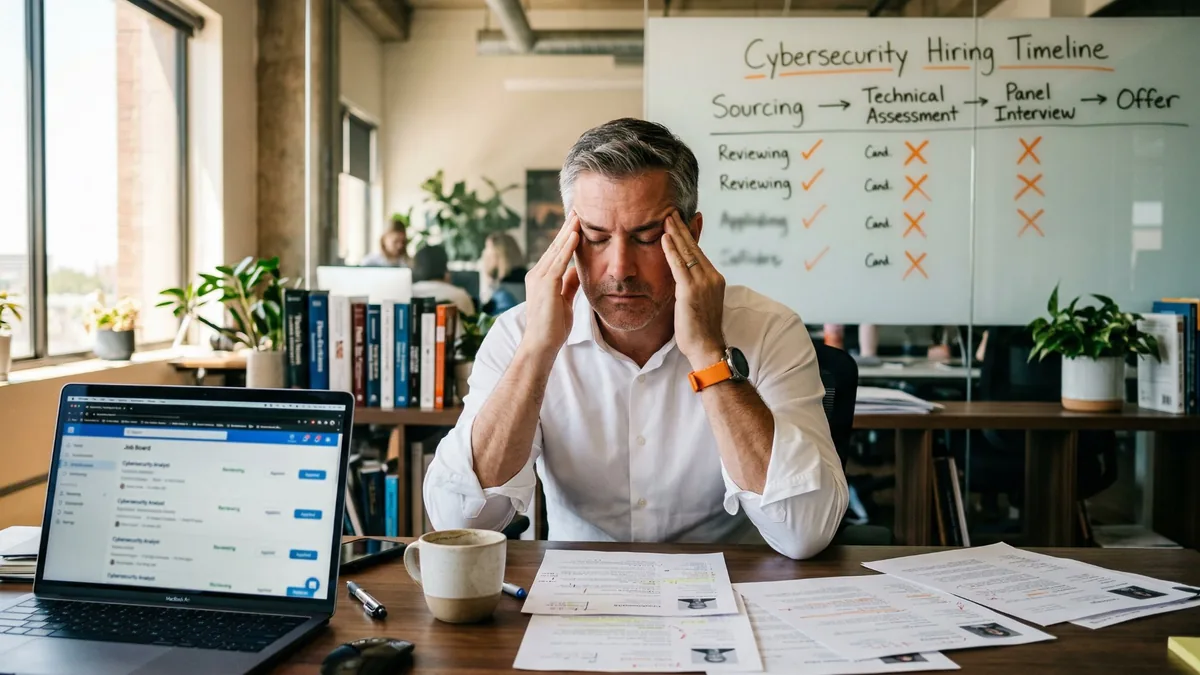
Frequently Asked Questions
How much does it cost to hire a cybersecurity professional in 2026?Wide range. Entry-level SOC analyst, $70K to $100K. Mid-level security engineer, $110K to $148K. If you need cloud security or architecture expertise, $128K to $220K depending on certs and experience level. CISOs are their own planet entirely. Total comp runs $250K to $700K at most organizations and the top 1% clear $3.2 million. If your numbers are from 2023, they’re wrong.What certifications should I look for?CISSP is the big one for senior roles. 22 to 35% salary premium. CISM if you’re hiring for management. CEH for pen testing. AWS or Azure security specialties for cloud. But here’s my actual advice. Don’t make certs your only filter. We’ve placed really strong security engineers who didn’t have their CISSP yet when they started. The cert shows someone studied. It doesn’t guarantee they can perform under real conditions. Use certs as one signal alongside experience, situational judgment, and references.Why does it take so long to hire security people?Three to six months is the industry average. It takes that long because the talent pool is tiny, the skills are specialized, and frankly most companies’ hiring processes have too many steps and too much dead time between them. The organizations that hire fastest get it done in three to four weeks. Not by cutting corners. By having their act together before the search starts.Should I use contractors or full-time hires?Both, probably. Full-time for core operations where you need deep institutional knowledge. Contractors for project-based work like pen tests, compliance audits, or covering a gap while you search. Contract-to-hire is the middle ground a lot of our clients end up choosing because you get to evaluate somebody in your actual environment before making a commitment. Honestly it’s one of the smartest hiring models in security right now.Why is the cybersecurity talent shortage so bad?4.8 million more openings than qualified people globally. Demand growing at 33% while the workforce barely grew at all last year. Budget constraints making it hard to pay competitive salaries. The specializations growing fastest, AI security and cloud security, are the ones with the fewest qualified professionals. And burnout is driving experienced people out of the field. It’s structural. More job boards won’t fix it.What actually keeps cybersecurity people from leaving?Team quality and manager quality, according to ISC2. That surprised me too when I first read it. Not comp, not title, not brand prestige. The people they work with every day and the person they report to. After that, career growth and learning investment. Keep their salary moving with the market at 7 to 10% annually. Watch for burnout symptoms. Give them a reason to see a future at your company. Do those things and you’ll outperform most organizations on retention. Which right now is a low bar, since half the industry can’t keep people.Build Your Security Team
The talent shortage is structural. It affects your risk profile directly. Every month a critical role sits open is another month of exposure you don’t need to accept.At KORE1, we fill cybersecurity roles for companies across the U.S. SOC analysts to CISOs. Contract, contract-to-hire, permanent. We know the market because we work in it every day.Talk to a KORE1 recruiter about your security hiring needs.Read full video transcript
Hiring cyber security engineers in 2026 means competing for a shrinking talent pool while threats grow more complex and budgets stay tight. ISC2 reported a global workforce of 5.5 million and a gap of 4.8 million with the workforce growing only 0.1% year-over-year while the gap grew 19%. This is what a lot of hiring teams are dealing with right now. The role has been open for months. Strong candidates disappear during interview delays. Compensation benchmarks are outdated before the search even gets moving. ISC2 says budget pressure is now one of the biggest drivers of staffing shortages with 36% of organizations reporting budget cuts, 24% reporting layoffs, and 49% of large organizations reporting hiring freezes. The headline number is the workforce gap, but the deeper issue is skills. ISC2 found that 90% of organizations report cyber security skills gaps and 88% experienced at least one significant cyber security consequence tied to those shortages. Nearly 70% experienced more than one. So this is not just a headcount problem. It is a capability problem. If your pay ranges were set using 2023 data, there is a good chance they are low. The BLS says the median annual wage was $124,910 in May 2024 and the top 10% earned more than $186,420. At the leadership level, overall CISO compensation rose 6.7% in 2025, while security budget growth slowed to 4%. This hiring pressure is not likely to ease soon. The Bureau of Labor Statistics projects 33% employment growth for information security analysts, which is much faster than average. That means demand should keep rising even as employers struggle to find the right skill sets. The skills shift matters more than ever. The non-negotiables are still network security, monitoring, incident response, and vulnerability assessment, but the high premium areas now include cloud security, AI security, and architecture skills that help organizations manage modern environments safely. ISC2's 2025 study specifically points to AI, cloud, and skills investment as key pressure areas. One of the biggest mistakes employers make is treating cyber security like one generic job category. It is not. Security analysts, security engineers, architects, penetration testers, incident responders, and CISOs all solve different problems. If the role definition is fuzzy, the search drags, the interview process gets messy, and the best candidates move on. When the market is this tight, the default hiring process stops working. The teams that close talent fastest do a few things well. They move quickly. They avoid overfiltering on background. They develop internal talent where possible, and they use contract or contract to hire models when the need is urgent or highly specialized. ISC2 also reports that many organizations struggle to keep security talent, so fit and speed both matter. The most expensive mistakes are usually avoidable. Unrealistic job descriptions, soft skills treated like an afterthought, outdated compensation data, and no serious retention plan. In cyber security, technical skill alone is not enough. Strong professionals also need to explain risk clearly, work crossf functionally, and stay composed under pressure. Keeping cyber security talent may be just as hard as hiring it. ISC2's 2025 workforce research highlights job satisfaction and skills investment as major themes. The takeaway is simple. When people do not see growth support or a sustainable workload, they start looking elsewhere. If you need one straightforward SOC analyst, and your team knows the market well, you may not need help. But when the need is urgent, a partner can change the outcome. The value is usually speed, access to niche talent, and market insight on compensation and process. The cyber security talent shortage is structural, and every month a critical role stays open is another month of unnecessary exposure. At Core 1, we help companies hire cyber security talent across the US on a contract, contract to hire, and direct hire basis. Talk to a Core 1 recruiter about your security hiring needs.


